Update:
Ellucian recently issued a joint statement with the Department of Education addressing the security alert. “Some of the issues mentioned in the alert may be unrelated to the vulnerability (Vulnerability) for which Ellucian released a patch on May 14, 2019. The Department and Ellucian have no reason to suspect that a breach has occurred as a result of this vulnerability.”
Original post
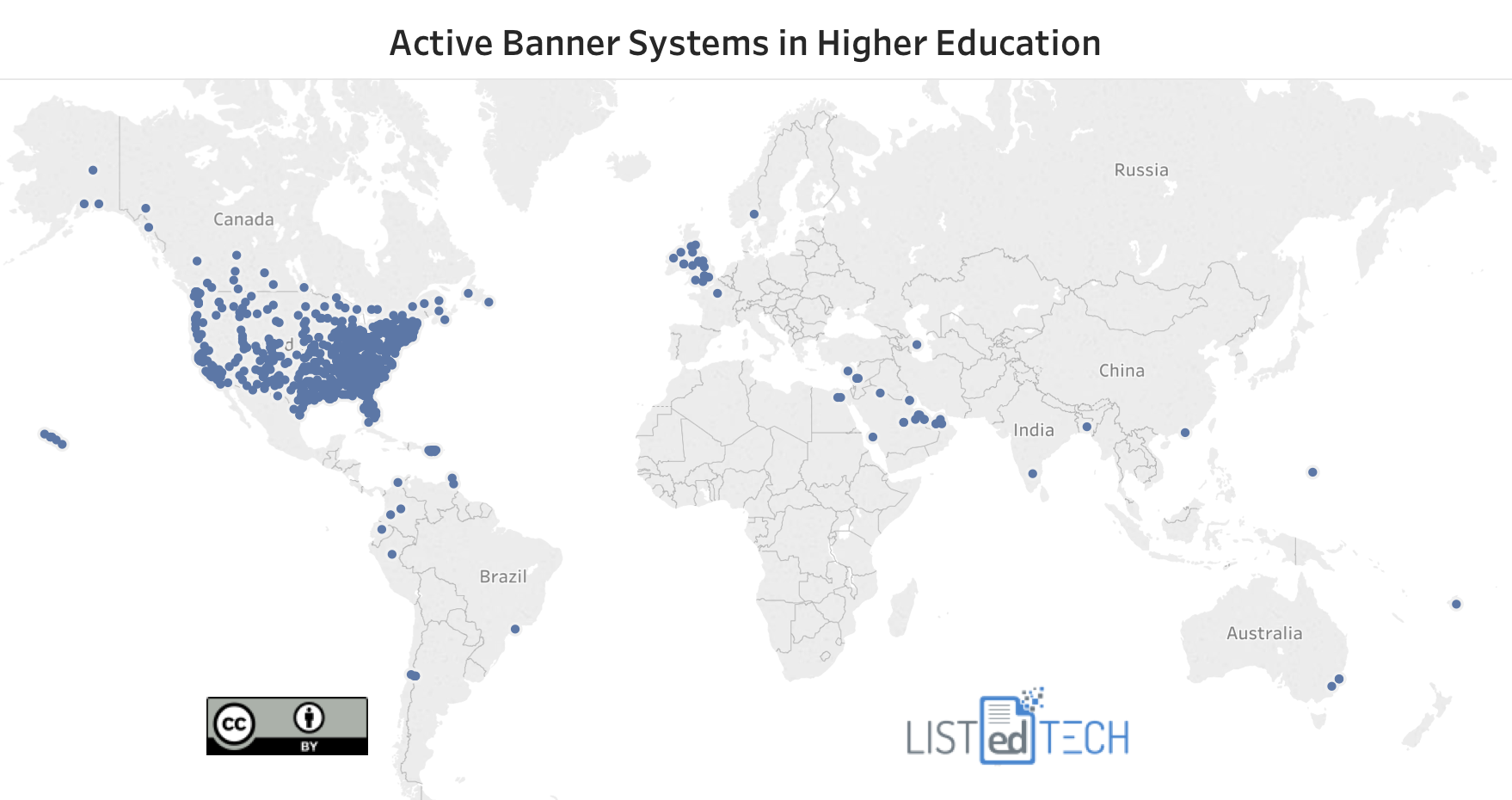
Ellucian’s Banner is one of the most popular ERP software used in HigherEd. Based on our data, it has a market share that is just under 25% in North America. For this reason, the news that came out this week about hackers who have been targeting a vulnerability in one of its modules is alarming.
Inside HigherEd describes the vulnerability: “Depending on the administrative privileges of the user, and the way data are organized by individual institutions, attackers could use this access to move laterally through administrative systems and access sensitive information.” “Ellucian fixed the vulnerability in May, and a public disclosure was published, by both the researcher and NIST” (ZDNet)
“According to Ellucian’s website, more than 1,400 institutions worldwide use Banner to manage student grades, staff payrolls, course schedules, admissions and student financial aid, among other tasks. Web Tailor and Enterprise Identity Services can be used by system administrators to get access to sensitive data protected under the Family Educational Rights and Privacy Act.” (Inside HigherEd) Authorities have mentioned that only older versions of Banner will be impacted. Institutions that have upgraded to Banner 9 should not be worried by potential attacks. As of July 20, 2019, 62 US institutions have reported attacks because of this vulnerability. (Koddos.net)
Although we don’t have all 1,400 institutions in our database (yet!), we do have 84% of them. Below is the global map of active implementations of Banner. As you can see, the vast majority of Banner users are in the US followed by Canada and the United Kingdom. They have an average enrollment of 8,856 students.